Data Security
When using the integration hub, you own and secure your data as required. The platform also provides features which allow users to effectively secure their data as needed. This includes authentication/authorization, data isolation, and encryption.
Read First!
Effectively securing data is complex. We recommend consulting a data security expert and ensure company/organization data management policies are being followed.
Our goal is to ensure our tools allow users to secure there data appropriately, however it is the responsibility of user to ensure their data is secured appropriately.
Our Data Policy
Our policy is very simple, you (the user) own and manage your data. We do not store or receive any of your data in our central servers (excluding metadata). In addition, we do not (and will not) sell data, metadata, aggregated data or any other user data or information. Our revenue model is based on providing premium services, not by selling data.
-
What data do we store?
- User logins and repositories (user passwords are hashed/salted)
- Database connection information. Database passwords are encrypted and can only be decrypted by the remote agents encryption key.
- General metadata and business rules such as jobs, schedules, and transforms
-
What we do not store?
- Encryption keys. These are stored with the locally installed remote agent.
- Raw & Processed data. Data processing occurs between the remote agent and the data sources only.
Data Isolation
Data isolation achieved by using firewalls and networks (and in some scenarios "air gaps") to create barriers between the data storage platform and unwanted users. The Integration Hub does not require data to be moved from these isolated areas.
-
Local Network Isolation
When the database is stored on the local network (but not available on the internet), a remote agent is installed on the local network which will perform the data processing remotely. -
Strict Isolation
When the database is on a highly secured network, which does not have outbound access to the central server, a development platform should be created outside this area to allow building and testing of data jobs. The tested jobs can be exported and run in isolation on the secured network. -
Publishing Isolated Data
When data is restricted to a local network, however there is a requirement to publish this outside the network, the Integration Hub provides an optional proxy server to allow this.
Encryption
Data Transmission
-
End User
All data between the user, and the web server or the remote agent and encrypted via SSL security certificates. The Integration Hub uses "Let's Encrypt" to automatically generate SSL certificates. If the connection has been explicitly set to not use encryption a warning will be displayed next to the remote agent. -
Remote Agent
The remote agent - database communication may or may not be encrypted depending on the features of the database being connected to. Best practices are to configure databases to encrypt data, or to ensure the remote agent/database connections are on a secured network.
Data Storage
-
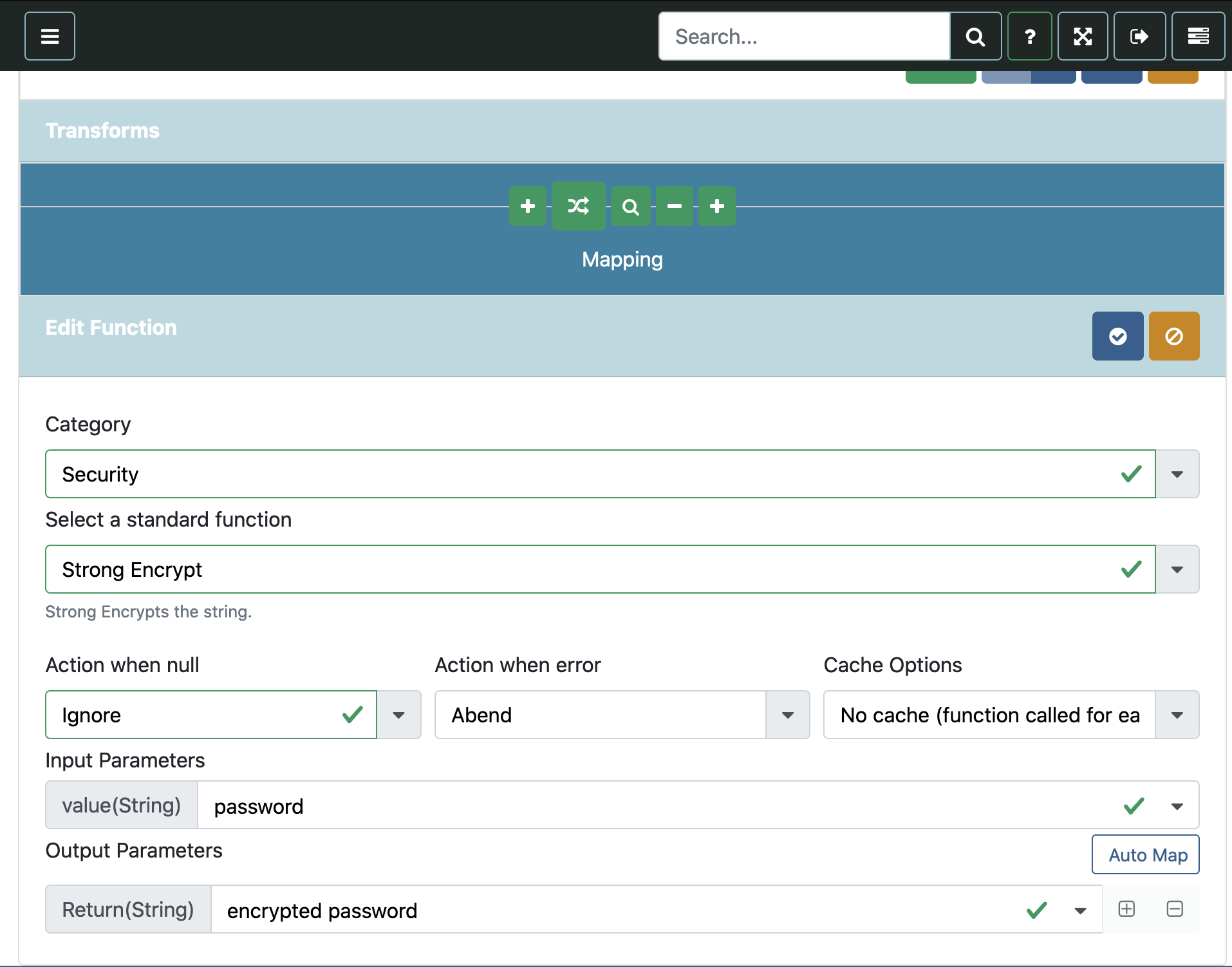
Encrypting Data
Data encrypted by the integration hub uses a composite encryption system where one part of the key is stored centrally and attached to each hub, and the other part of the key is stored with the remote agent. This ensures that if either the central web store or the remote agent are compromised the encrypted data will still be safe. -
Column Encryption
Individual columns can be encrypted by specifying the security flag on the column metadata. This provides the following options:-
Fast Encrypt - Performs a 5 iteration, salted encryption.
-
Slow Encrypt - Performs a 1000 iteration, salted encryption.
-
Hash - Securely hashes/salts the field.
-
Password Encryption
Passwords which are used to authenticate database connections are stored centrally with a slow/salted encryption. When exporting or migrating hubs, only the encrypted values are exported. -
Variable Encryption
Variables which have the "Encrypt" option specified are stored centrally with a slow/salted salted encryption. When exporting or migrating hubs, only the encrypted values are available.